& Blogs
News & Blogs

April 28, 2026
Why GenAI Proof of Concepts Fail in Production and How to Fix It
Moving from the early success of a promising GenAI demo/proof of concept to a reliable, scalable solution used every day across the business is often where the real challenge begins.
.png)
April 15, 2026
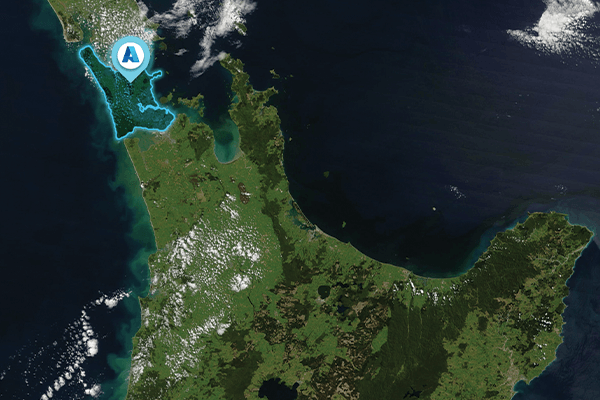
Theta Adventure Racers Take on Kaikōura for Cure Kids
Our Theta Adventure Racers were back in action this month as they tackled the Kaikoura Adventure Race. This epic multisport challenge featured hiking, mountain biking, pack rafting, and navigation through the stunning Kaikōura region.
.png)
April 15, 2026
Can Your People Spot a Vishing Attack in Real Time?
Attackers are increasingly targeting service desk and contact centre teams with convincing phone-based social engineering attacks designed to bypass security controls. Would your people recognise a vishing (phone-based phishing) attempt and respond correctly in the moment?
.png)
March 26, 2026
Educating Whānau on Cyber Security: A New Weekly Series
Introducing Kiisha-Rose Woodhouse’s weekly Cyber Series, launched as part of her internship and the Theta Te Ao Māori Technology Scholarship.

January 22, 2026
Watch Now — The Innovation Circuit EP 9: A guide to data protection with Microsoft Purview during the AI revolution
In this episode, we’ll be discussing how to ensure your organisation’s sensitive data remains secure and confidential with Microsoft Purview.

November 12, 2025
What's New in Dynamics 365 Business Central 2025: wave 2
Watch the Dynamics 365 Business Central update with Head of Dynamics 365, Joerg Rau.
.png)
August 21, 2020
Theta Analytics is now Theta Data and Insights
Theta Analytics is now Theta Data & Insights, better reflecting the need to dive deeper in complex environments, uncover the ‘hows’ and ‘whys’ of what you see and make the right decisions based on those conclusions. In effect, organisations today need more than analytics; they need insights to act on.
%20(1).png)
August 6, 2020
2019-20 Annual Report Published
Our annual report for 2019-2020 is here. An overview of activity, performance and highlights for the financial year ending 31 March 2020.
%20(1).png)
August 6, 2020
Part 3: Analysing MedusaLocker ransomware
(Part 3 of 3) In this 3-part post, we share the tradecraft from an RDP brute force linked ransomware event (MedusaLocker) we responded to in June 2020. We cover the business ramifications of the attack, technical analysis and some advice based on attacks such as these. Continued from parts 1 and 2...
.png)
August 5, 2020
Part 2: Analysing MedusaLocker ransomware
(Part 2 of 3) In this 3-part post, we share the tradecraft from an RDP brute force linked ransomware event (MedusaLocker) we responded to in June 2020. We cover the business ramifications of the attack, technical analysis and some advice based on attacks such as these. Continued from part 1...
.png)
August 4, 2020
Part 1: Analysing MedusaLocker ransomware
In this 3-part post, we share the tradecraft from an RDP brute force linked ransomware event (MedusaLocker) we responded to in June 2020. We cover the business ramifications of the attack, technical analysis and some advice based on attacks such as these.
%20(1).png)
July 31, 2020
Tech-savvy kids take on Mixiply
Jim Taylor has just finished co-presenting at the STEM education summit and Serious Play Conference with Marianne Malmstron, Digital Technologies teacher at Newlands Intermediate School. For the past three years, he’s been using his incredible knowledge to help kids around the 11-13 age group learn about technology; in particular, Mixed Reality. This learning has been taking place through an app called Mixiply.
.png)
July 27, 2020
Cyber exploitation at scale: don't become a victim of remote access exploitation
Let’s face it – it’s been a tough period for remote access solutions, especially when we’re so dependent upon it. First, we had the myriad of SSL-VPN’s from the likes of Cisco, F5, Palo Alto, Cisco, Fortinet and Pulse Secure – going from being an enterprise security product to the worst nightmare for a security team overnight.
.png)
June 18, 2020
Mitigating remote working security risks
It's not just about the basics, there are new emerging threats and risks when it comes to shifting to more remote styles of working.
%20(1).png)
June 15, 2020
UX Analytics: tools, testing and pro tips
“Normal work” has been changing a lot for people working in customer experience! Many UX designers are working from home and might do so for a while. This means you’re probably adjusting the way you collaborate and undertake research - including using Miro boards, real-time ‘co-editing' within your Adobe XD document and Teams/Zoom user interviews.




.jpg)

%20(1).png)


.png)


.png)